In Kenya’s digital economy, a phone number is not merely a communication tool; it is a digital identity, a business storefront, and a bank account. Through M-Pesa, it holds the KES needed for daily survival. So, what happens when a user loses their phone in a catastrophic accident, loses their mobility, and is systematically locked out of their own life by the very security protocols designed to protect them?
Over the past 24 hours, a harrowing exchange on X (formerly Twitter) between a Kenyan user and Safaricom’s official customer care handle has ignited a fierce debate about the empathy gap in modern telecommunications. It highlights a critical blind spot in the industry’s war against fraud: the complete lack of a standardised edge-case protocol for the physically incapacitated.
Catch-22
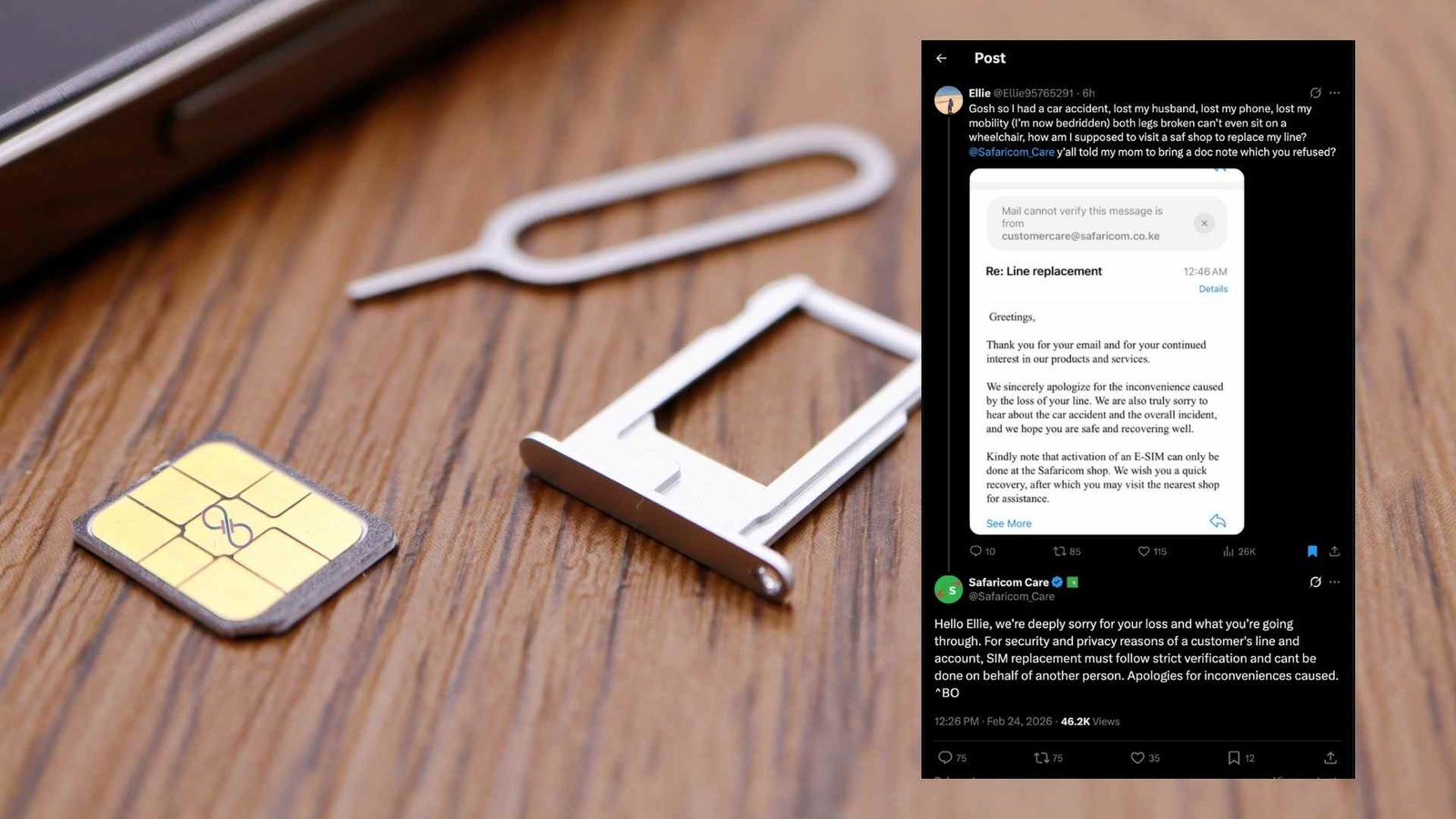
The narrative unfolding online is a nightmare of digital exclusion. An X user named Ellie (@Ellie95765291) stated they were involved in a severe car crash that claimed their husband’s life and left them bedridden with two broken legs. Having lost their phone in the wreckage, they require a SIM replacement to access their M-Pesa funds for medication and to salvage their business.
They requested an eSIM activation via email—a standard modern workaround. However, because their secondary Apple email requires two-factor authentication from the lost phone number, they are trapped in a classic technological catch-22.
When their mother reportedly presented a doctor’s note to a Safaricom shop, it was rejected. Safaricom’s official, public response on X remained rigidly procedural: “For security and privacy reasons of a customer’s line and account, SIM replacement must follow strict verification and cant be done on behalf of another person.”
This is not just a customer service failure; it is a systemic architectural flaw. When a multi-billion shilling corporation automates its empathy, substituting a human bridge with cold, scripted responses, it disenfranchises the most vulnerable.
KYC Regulations
To critically analyse this, one must acknowledge why this wall exists. Kenya has been ground zero for devastating SIM-swap fraud. Cybercriminals routinely deploy sophisticated social engineering tactics to hijack phone lines. Once in control, they drain M-Pesa accounts and secure mobile loans, leaving victims financially ruined.
In response, the Communications Authority of Kenya (CA) and telcos implemented draconian Know Your Customer (KYC) protocols. The prevailing rule is absolute: a customer must be physically present with an original ID, and a live photograph must be captured.
From a purely risk-management perspective, Safaricom’s system is functioning exactly as engineered. It is a blunt-force shield designed to reject any proxy attempt. But in the pursuit of absolute security, the telecommunications giant has created a system devoid of exceptions.
Update: Safaricom caved to pressure and assisted
The Hypocrisy of “Physical Presence”
The public backlash on X was immediate and illuminating, pointing out a glaring operational contradiction. Netizens accurately noted that Safaricom routinely dispatches sales representatives door-to-door to market Home Fibre connections.
If a company with immense logistical capabilities can mobilise agents to acquire new revenue, why is it technologically or operationally impossible to deploy a specialised agent equipped with a biometric scanner to verify the identity of a bedridden customer?
Furthermore, the banking sector – which handles strictly regulated financial assets – has long-established protocols for incapacitated clients, such as secure home visits by bank managers or the acceptance of a legally drafted Power of Attorney. Safaricom, which operates the world’s most successful mobile money platform, seemingly lacks a comparable digital identity solution for severe medical emergencies.
Designing for the Edge Case
This incident is a wake-up call for the African tech ecosystem. Security and accessibility cannot remain mutually exclusive. The solution does not require dismantling anti-fraud measures; it requires building sophisticated, human-centric contingencies.
- Authorised Institutional Verification: Telcos could establish secure, cryptographic communication channels with recognised hospital administrators. If a patient is verified by a chief medical officer, that institution should be able to act as a trusted node for digital identity verification.
- Mobile e-KYC Rapid Response: For demonstrably bedridden clients, telecommunications companies should offer a secure, mobile verification unit. A representative equipped with biometric tools and real-time access to the Integrated Population Registration System (IPRS) could safely replace a SIM card at a hospital bedside or home.
- Advanced Remote Biometrics: Utilising secure, highly encrypted video-link verification paired with real-time facial recognition – a standard already employed by global digital-only banks like Monzo or Revolut – could bypass the need for physical retail visits entirely.
The Bottom Line
Protecting users from SIM-swap fraud is a non-negotiable necessity. But a security protocol that actively prevents a grieving, bedridden individual from accessing their medical funds is a broken system.
Technology is meant to be an enabler, not a barrier. Until telecommunication giants learn to categorise and resolve these edge cases with the nuance and humanity they require, they risk remaining corporate behemoths that connect lines, but disconnect from the reality of the people using them.